Summary: Low-code and no-code (LCNC) platforms have empowered millions of business users to build apps, automate workflows, and connect data sources -without writing a single line of code. But this productivity revolution comes with a serious security blind spot. This article explores the phenomenon of ‘shadow engineering,’ the security risks it creates, how the market is responding, and why purpose-built platforms like Nokod Security are redefining enterprise application security.
The No-Code Explosion: Opportunity Meets Risk
The low-code/no-code (LCNC) market has undergone a dramatic transformation over the past decade. What began as a tool for rapid prototyping and departmental automation has evolved into a full-blown enterprise development paradigm. According to Gartner, by 2026, developers outside traditional IT departments will account for at least 80% of the user base for low-code development tools-a staggering shift in who is actually building enterprise software.
Finance teams are automating reporting workflows. HR departments are designing onboarding apps. Operations managers are stitching together integrations between CRMs, ERPs, and cloud storage-all without involving a single professional developer. Platforms like Microsoft Power Platform, Salesforce, ServiceNow, UiPath, and Retool have made this easier than ever.
The result is an enterprise app ecosystem that is growing faster than anyone anticipated-and faster than traditional security teams can keep up with. This is where a dangerous new trend emerges: shadow engineering.
What Is Shadow Engineering?
Shadow engineering is the practice of business users-often called citizen developers-building functional applications, automations, and integrations outside the formal oversight of IT and security teams. It is the natural evolution of shadow IT, but with a critical difference: these users are not simply using unsanctioned SaaS tools. They are actively building and deploying software that touches sensitive corporate data, customer records, and critical business processes.
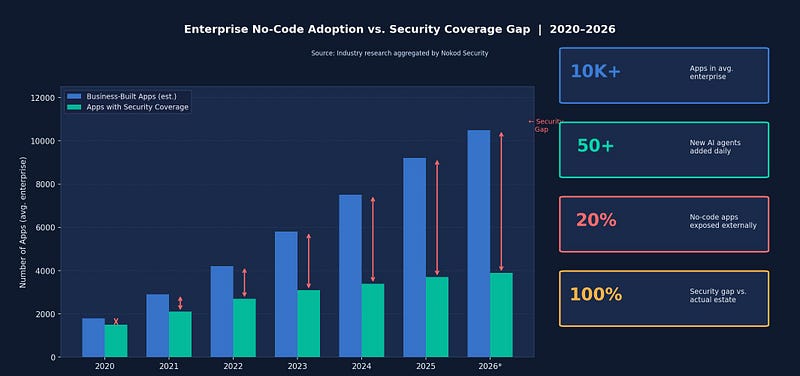
The scale of shadow engineering in modern enterprises is staggering. Research suggests that large organizations may have:
• 10,000 or more apps built on no-code platforms in a single enterprise environment
• Dozens of new AI agents added to workflows every single day
• As many as 20% of no-code apps exposed externally-to customers, partners, or the public internet
• A significant gap between what security teams estimate exists and what is actually running in production
None of these assets went through traditional application security review. Many are not documented. Most are invisible to AppSec teams until something goes wrong.
The Security Risks Behind the Convenience
Shadow engineering creates a wide and largely unmonitored attack surface. The security risks are not hypothetical-they are structural and systemic. Key vulnerabilities include:
• Data leakage: Business-built apps often connect to sensitive data stores -SharePoint, Salesforce, Dataverse-without proper access controls, creating pathways for data to flow to unintended destinations.
• Hardcoded secrets: Citizen developers frequently embed API keys, credentials, and connection strings directly into app logic, creating persistent exposure risks.
• Excess permissions: No-code automations often run with over-privileged service accounts, violating the principle of least privilege.
• Injection attacks: Unvalidated inputs in low-code forms and flows can expose organizations to SQL injection and prompt injection attacks.
• Supply chain vulnerabilities: Custom connectors and third-party integrations built by non-developers often lack security vetting, introducing untrusted dependencies into the enterprise stack.
• Orphaned assets: When employees leave or change roles, the apps and automations they built often continue running-unowned, unmonitored, and unremediated.
How the Market Is Responding
The security industry has begun to recognize LCNC as a distinct and urgent threat domain. Several categories of tools have emerged to address parts of the problem:
Traditional application security (AppSec) tools-built for professionally written code-struggle to analyze or even discover no-code assets. Cloud Access Security Brokers (CASBs) and Data Loss Prevention (DLP) tools offer some coverage at the network level, but cannot inspect the logic inside low-code flows or agents. Identity and Access Management (IAM) tools can help with permissions but lack visibility into how those permissions are being used within citizen-built applications.
Some platform vendors have introduced native governance features -Microsoft’s Power Platform admin center, for example, offers policy controls and usage analytics. But these are platform-specific and cannot provide a unified view across the multi-platform environments that characterize most large enterprises.
For broader context on the evolving landscape of enterprise shadow IT risk, the Cloud Security Alliance provides in-depth research and guidance on detection and governance strategies.
Nokod Security: Built for the No-Code Reality
This is precisely the gap that Nokod Security was designed to fill. Nokod’s security platform provides enterprises with visibility and control over business-built apps, automations, and AI agents-without slowing innovation.
According to Nokod, the average enterprise environment contains more than 10,000 apps built on no-code platforms, with over 50 new AI agents added daily. Yet security teams are rarely aware of more than a fraction of these assets. Nokod addresses this by automatically discovering and mapping all LCNC apps and flows across every supported platform, giving security teams one clear view of every environment, integration, and data path.
The platform is built to serve two audiences simultaneously: AppSec teams who need deep technical insight into vulnerabilities, and the business users who built the apps in the first place. For the latter, Nokod offers one-click remediation-simple, actionable guidance that does not require developer expertise to implement.
Nokod supports major enterprise LCNC environments including Microsoft Power Platform, Copilot Studio, Salesforce, UiPath, ServiceNow, and Retool-making it one of the most comprehensive platforms available for this use case.
Why This Matters Now
The urgency of the shadow engineering problem is only increasing. As organizations accelerate their digital transformation efforts and adopt AI agents to automate ever more complex tasks, the volume and complexity of citizen-built assets will continue to grow. Regulatory pressures-including GDPR, HIPAA, PCI-DSS, and emerging AI governance frameworks-are also raising the stakes for organizations that cannot demonstrate control over their full application inventory.
Security leaders who ignore shadow engineering today are setting themselves up for material breaches tomorrow. The combination of unvetted app logic, over-privileged access, and sensitive data connections represents exactly the kind of systemic vulnerability that threat actors seek to exploit.
Conclusion
The no-code revolution is not going away. Business users will continue to build, automate, and connect-and that is fundamentally a good thing for organizational agility. But agility without security is a liability. Shadow engineering is the defining enterprise security challenge of the LCNC era, and it demands a purpose-built response.
To understand how leading enterprises are managing shadow it security risks in LCNC environments, Nokod Security offers deep-dive resources and a platform built by AppSec veterans who actually understand what’s at stake.